The Cyber Resilience Act (CRA) places long term security and maintenance responsibilities on manufacturers that develop and maintain the connectivity used in industrial devices and machines1. In our previous two articles (CRA is redefining industrial connectivity and CRA is painful, but necessary) , we explored what those responsibilities look like and why the CRA is necessary, even though it introduces new expectations, processes, and lifecycle obligations.
This third article moves from why to how.
It explains why legacy connectivity is difficult to make CRA-compliant, and how achieving CRA compliance becomes much easier for industrial device makers and machine builders if they replace older connectivity with a modern, CRA ready connectivity solution.
Let’s start with a key question: What makes older connectivity solutions so difficult to align with CRA?
Legacy, in house, or custom connectivity solutions were never designed for CRA. Most were built when the focus was on functionality, not cybersecurity, documentation, or lifecycle obligations. CRA exposes gaps that are difficult, sometimes impossible, to fix retroactively.
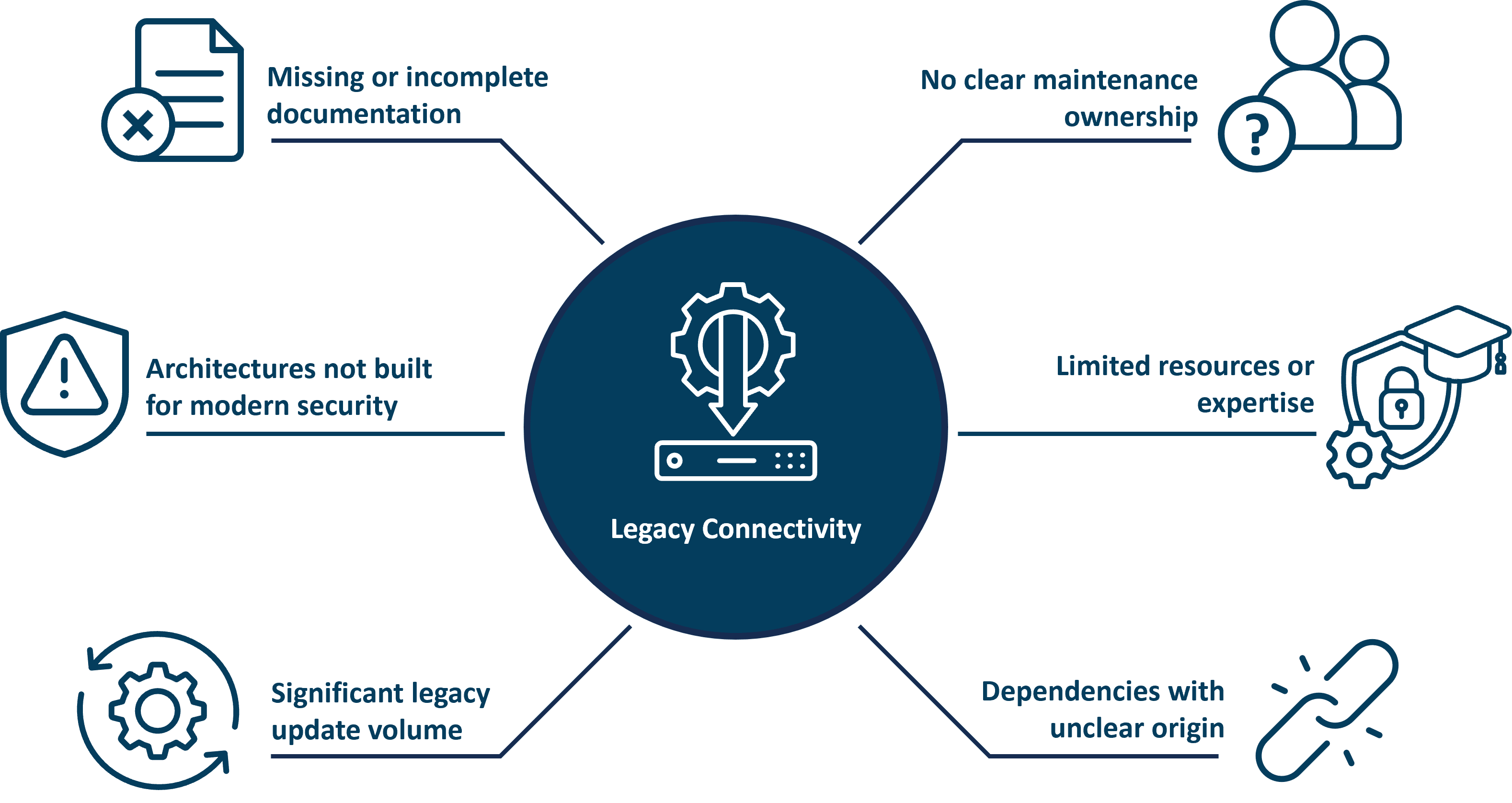
Figure 1. Legacy connectivity was not designed for the long-term security, documentation, and lifecycle obligations required by CRA.
Here are some of the common issues that HMS have encountered over the years:
Older connectivity stacks often lack:
CRA requires all of this.
Responsibilities often drift over time. Without a defined owner:
CRA requires structured security engineering and continuous documentation. Many teams lack:
Legacy connectivity often contains:
CRA requires complete traceability which is difficult with older dependencies.
These challenges are amplified when CRA must be applied across entire product portfolios.
In industrial automation, product lifecycles are long. Devices and machines often remain in production for 15–20 years or more. As a result, CRA compliance is rarely limited to a single new design.
Device makers and machine builders are often faced with:
At the same time, updating the host application, which contains the core product software and functionality, is already a major task. Taking on full CRA conformity work for legacy connectivity on top of this quickly stretches internal resources.
CRA applies to the complete device or machine. In practice, however, connectivity is typically the most complex and resource intensive part to bring into compliance.
Connectivity often includes:
Because so many CRA requirements concentrate in this area, outsourcing CRA conformity work for connectivity can significantly reduce the overall compliance effort.
Older stacks may lack:
Retrofitting these late in the lifecycle is costly and sometimes technically unfeasible.
In short: Legacy connectivity becomes a bottleneck because it was never intended to meet the expectations CRA now defines.
Legacy connectivity makes CRA compliance challenging, but a modern, CRA ready connectivity solution can simplify much of this work.
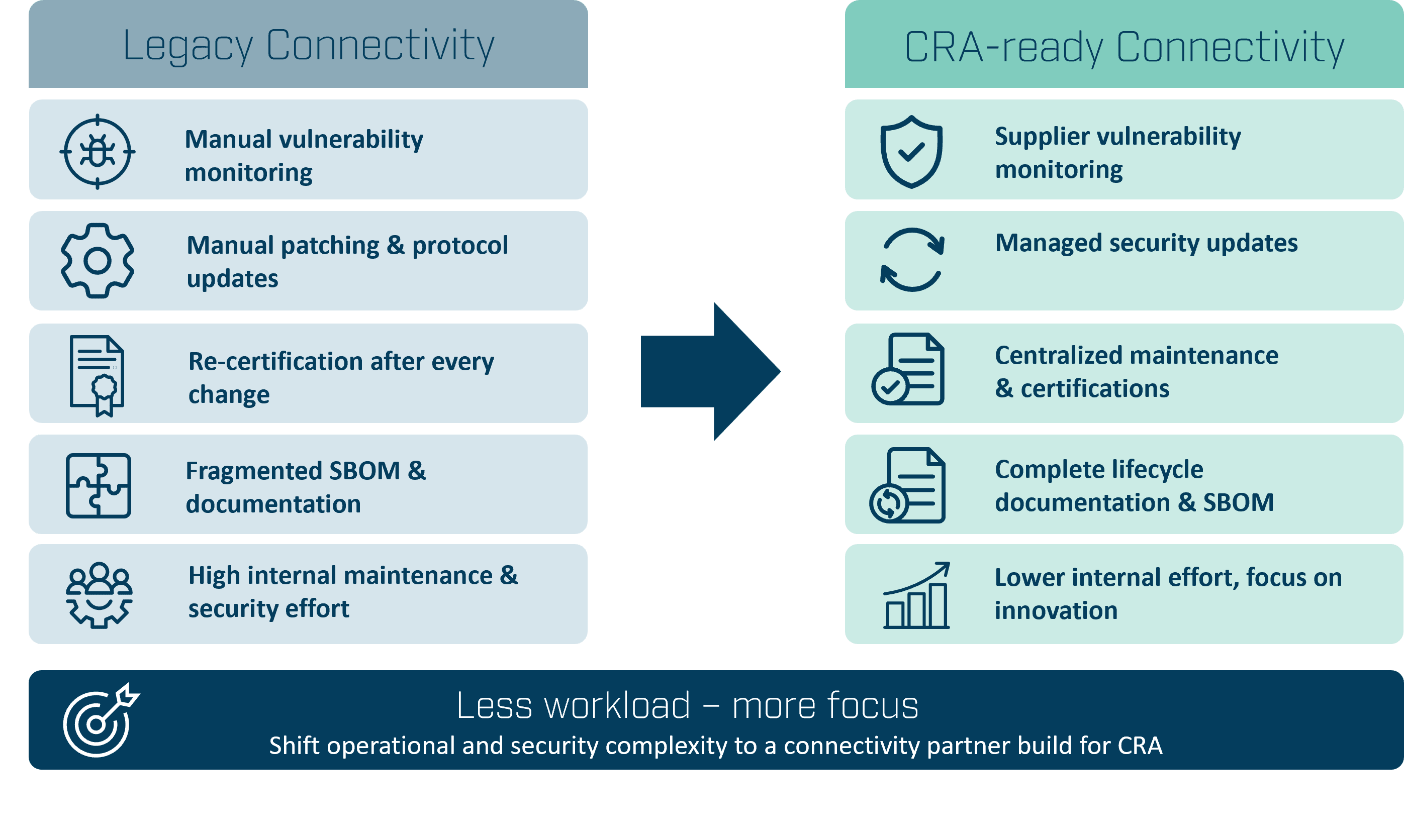
Figure 2. Replacing legacy connectivity shifts much of the CRA-related security and maintenance workload away from the manufacturer.
Before diving into specifics, it is worth asking:
Replacing in house or outdated connectivity with a modern, CRA ready communication interface or gateway shifts most of the operational and security workload away from the device maker or machine builder.
With a ready made solution, core CRA responsibilities are handled by a supplier whose products and processes are built specifically for long term security and compliance.
Suddenly, the following becomes a lot easier for device makers and machine builders:
Modern connectivity solutions include well defined update mechanisms, documented processes, and streamlined release cycles. Software patches can be delivered faster, more securely, and with predictable quality.
Instead of building and maintaining secure development processes in house, manufacturers can rely on a connectivity supplier who already operates compliant processes and provides the necessary evidence.
With a CRA ready connectivity solution, responsibilities are clearly divided:
This eliminates ambiguity and reduces the amount of internal coordination required.
Modern connectivity solutions are designed to meet evolving standards. As CRA guidance, harmonized standards, and market expectations continue to evolve, manufacturers benefit from ongoing supplier support instead of managing change alone.
Moving to a CRA ready connectivity solution eliminates a significant amount of technical and organizational work. Below are the most resource intensive tasks device makers and machine builders avoid.
Legacy stacks require continuous updates to:
A CRA ready solution shifts this entire maintenance burden to the supplier.
Manufacturers no longer need to track:
The connectivity supplier handles vulnerability monitoring and communication.
Secure boot, firmware signing, update validation, rollback protection, and audit trails become the supplier’s responsibility.
Any significant update to an in house stack could trigger renewed testing or re certification. A CRA ready solution manages this overhead centrally, reducing rework.
Manufacturers no longer need to gather CRA declarations from dozens of chip, OS, or library suppliers. The connectivity component itself provides the required CRA documentation.
Replacing legacy connectivity means device makers and machine builders no longer maintain communication security themselves. Instead, they adopt a solution that delivers:
Out of the box.
This lets teams focus on product integration rather than connectivity maintenance.
Reducing CRA effort does not mean transferring full responsibility2.
Even the best connectivity solution does not eliminate all CRA obligations. Device makers and machine builders remain responsible for CRA compliance of the complete product.

Figure 3. Effective CRA compliance depends on clearly defined responsibilities.
What changes is the workload distribution. A large portion of the work required to make connectivity CRA ready can be performed by the connectivity provider, while the manufacturer retains responsibility for the overall product.
Device makers and machine builders remain responsible for the following:
Connectivity must be integrated correctly:
This is always the manufacturer’s job.
CRA requires manufacturers to understand how their complete product behaves in its intended environment. including:
Manufacturers must provide:
Transparency across the lifecycle is mandatory under CRA.
In summary, a ready made connectivity solution dramatically reduces the technical complexity of CRA, but it does not replace the manufacturer’s role in delivering a secure product.
This raises a final question for manufacturers preparing for CRA:
What does a realistic, sustainable approach to CRA compliance look like?
Legacy connectivity makes CRA compliance difficult because it was never designed for long term security, documentation, or lifecycle responsibilities.
Replacing it with a modern, CRA ready connectivity solution removes many of the most demanding obligations3, including:
Manufacturers still own system level security and product integration, but using a CRA ready connectivity solution provides a more reliable, more efficient, and more sustainable path to compliance.
In the next article, we will examine why CRA obligations force organizations to rethink how connectivity is structured, owned, and maintained, and why this becomes a strategic decision.
Whether you are updating existing devices or designing new ones, the right connectivity strategy is key to CRA readiness. Learn more about the Cyber Resilience Act and explore Anybus gateway and embedded solutions that help you build secure, maintainable, and future-ready devices.
Dr. Jens Jakobsen
Product Security Manager, HMS Networks
Dr . Jens Jakobsen is Product Security Manager at HMS Networks, where he leads the company’s work to strengthen the cybersecurity of industrial communication products and protect connected equipment from emerging threats. He brings extensive experience from technical and leadership roles at HMS Networks, Schneider Electric, and Motorola Solutions, and has worked for many years with industrial communications and cybersecurity. Dr. Jakobsen holds seven granted patents in telecom and industrial communication technologies.
References
1. Cyber Resilience Act implementation - Frequently asked questions
https://digital-strategy.ec.europa.eu/en/library/cyber-resilience-act-implementation-frequently-asked-questions
2. Cyber Resilience Act - Conformity assessment https://digital-strategy.ec.europa.eu/en/policies/cra-conformity-assessment
3. European Commission – Draft guidance on the application of the Cyber Resilience Act : https://ec.europa.eu/info/law/better-regulation/have-your-say/initiatives/16959-Draft-Commission-guidance-on-the-Cyber-Resilience-Act_